In today’s digital-first architecture, Application Programming Interfaces (APIs) have evolved from internal code connectors to the backbone of modern applications. APIs now power everything from microservices and mobile apps to cloud integrations and B2B platforms. According to research, over 83% of all internet traffic comes from APIs (Akamai, 2023)—highlighting just how critical they are for enterprise operations.
This exponential growth has unlocked innovation but also widened the attack surface. Traditional security controls that worked for web apps fall short in this API-first economy (OWASP API Security Top 10). Today, executives must understand not only classical injection exploits, but also subtle manipulations of workflows—known as Business Logic Attacks (BLAs).
Major API Attack Vectors: Embedded vs. Business Logic Exploits
Embedded Attacks
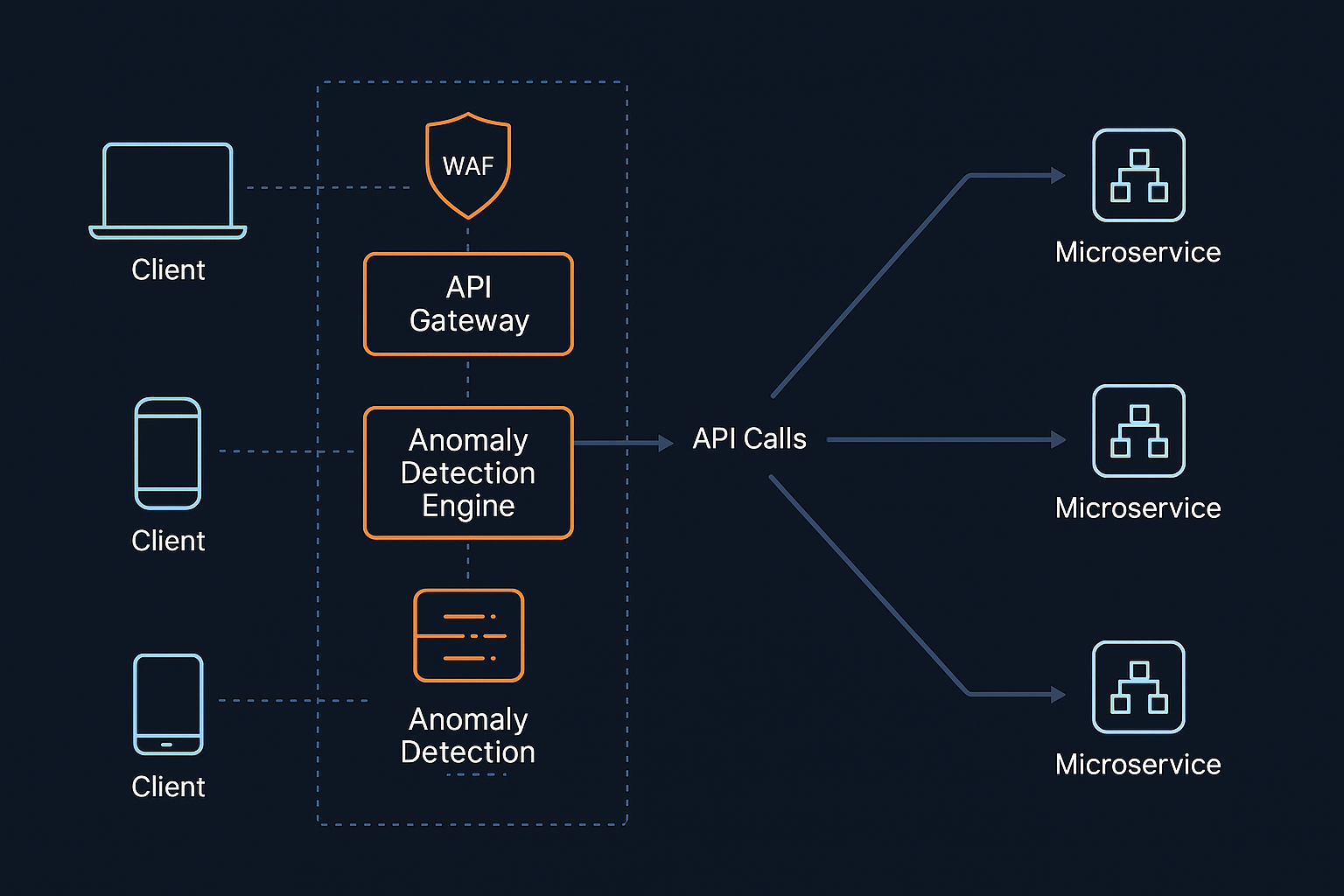
Embedded attacks focus on exploiting technical flaws in the API or its infrastructure. These include SQL injection, weak authentication bypass, or abusing outdated libraries. Such attacks are usually recognizable (e.g., malicious payloads) and are often caught by WAFs or API gateways (Cloudflare API Security Overview).
Business impact: Data breaches, downtime, regulatory penalties.
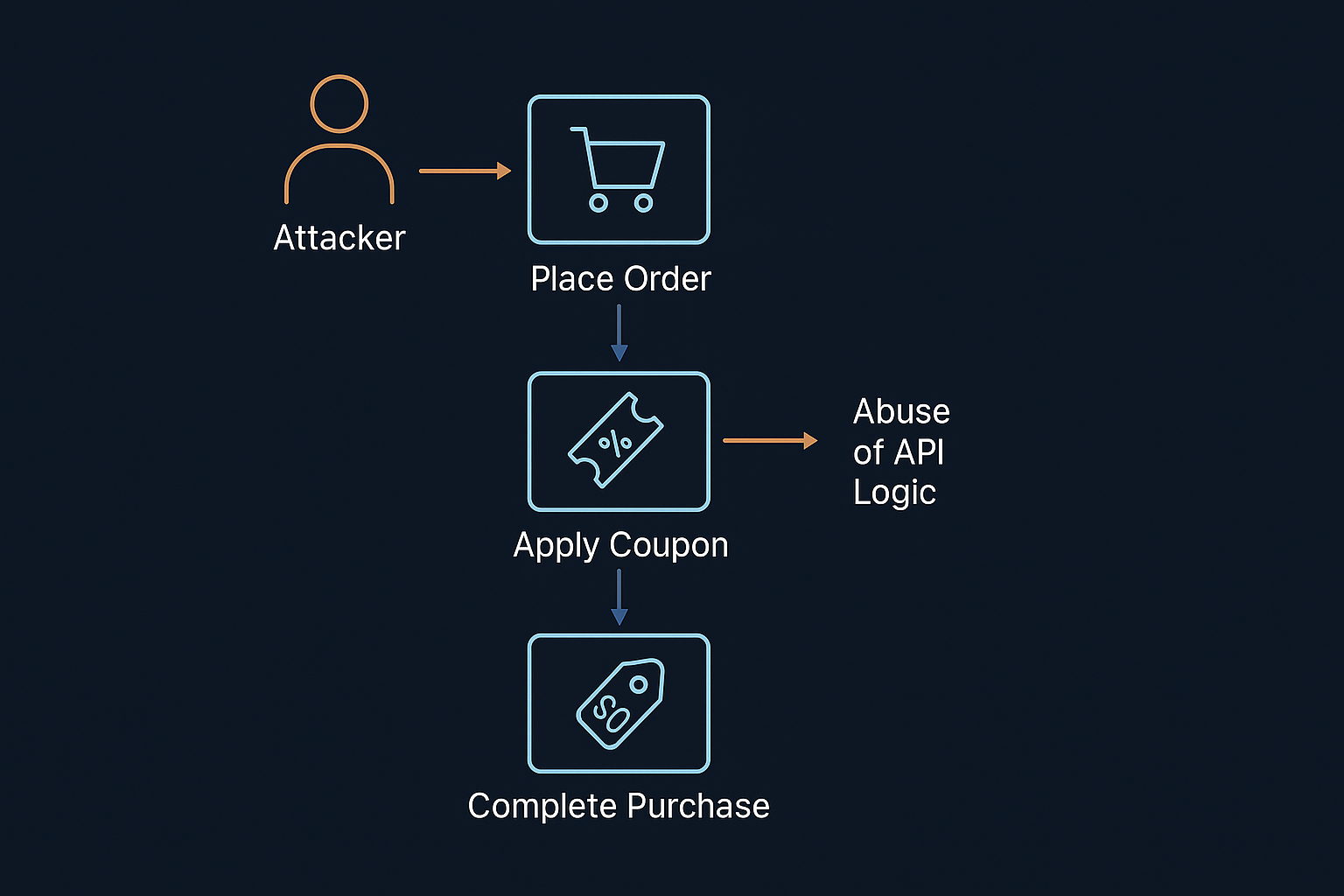
Business Logic Attacks (BLA)
BLAs don’t target code weaknesses but rather exploit the way APIs handle logic. For example:
-
Applying a discount coupon multiple times to reduce costs to zero.
-
Bypassing rate limits to scrape sensitive datasets.
-
Manipulating order workflows to enable fraud.
Because these calls look legitimate, they often bypass signature-based detection.
Business impact: Revenue loss, fraud, brand damage, and customer data exposure.
Challenges in Protecting APIs
Protecting APIs—especially from BLAs—comes with unique challenges:
-
Limited Visibility: Shadow APIs and poor documentation mean security teams often don’t know what exists.
-
Complex Workflows: Multi-step transactions make it hard to track misuse across sequences.
-
Normal Appearance: BLA requests mimic real traffic, evading rules and alerts.
-
Sophisticated Adversaries: Attackers now use AI-driven reconnaissance to map APIs and exploit logic faster than ever.
Must-Have Capabilities for Comprehensive API Protection
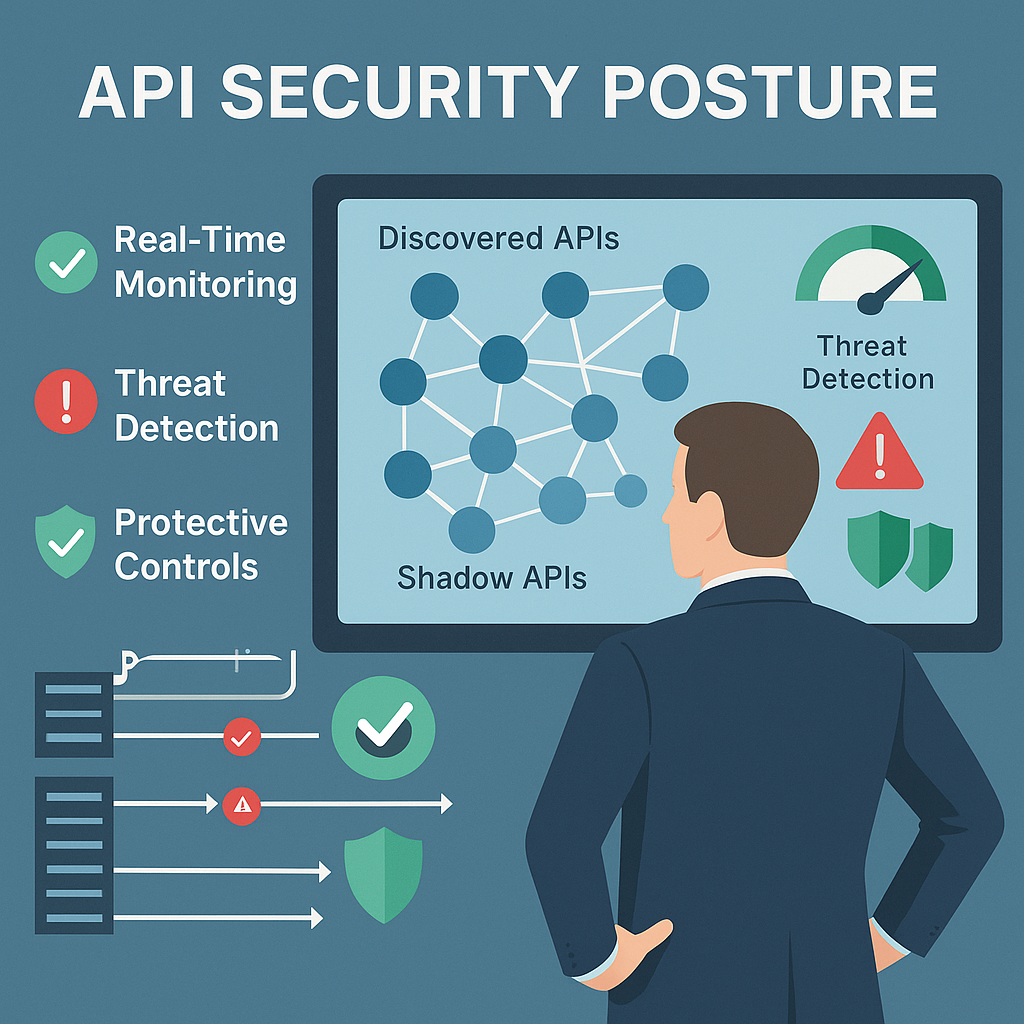
To secure API-driven systems, organizations must focus on:
-
Granular Discovery: Automated mapping of all APIs, including undocumented shadow APIs.
-
Behavioral Analysis: ML-driven anomaly detection to baseline normal API use.
-
Business Logic Mapping: Real-time tracking of workflows across endpoints.
-
AI-driven Policy Automation: Adaptive security policies generated from live traffic.
-
Strong Enforcement: Runtime blocking with support for custom business logic rules.
-
Real-Time Mitigation: Instant detection and prevention of attacks without false positives.
-
Cross-Layer Correlation: Integrating API defense with WAF, DDoS, and bot mitigation for layered resilience (OWASP API Security Guidance).
Conclusion
APIs are no longer just technical plumbing—they are strategic business assets. Their security is now directly tied to customer trust, revenue protection, and regulatory compliance.
As a technology leader with two decades in development and delivery, my perspective is clear: organizations that treat API security as board-level risk management will thrive in the API economy. The challenge is steep, but by adopting a multi-layered API protection posture, enterprises can stay ahead of adversaries while keeping APIs a secure foundation for innovation.